How scammers are holding IT users to ransom
When we consider the term ‘Ransom’, we immediately imagine a kidnapping scenario whereby money is demanded in return for the safe exchange of the victim. However, in technological terms, a Ransom refers to the fee expected from unscrupulous scammers to restore your PC to a usable state.
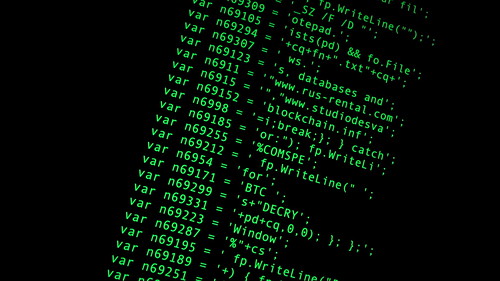
Ransomware is on the rise, and scammers are reaping the benefits of a growing trend in demanding money with menaces. The malicious software attacks PCs in aggressive ways, downloading pornography or encrypting files to make the computer unusable. Once the virus has downloaded, users can find themselves powerless to eradicate the offensive image or corrupt data. At this point, the scammers demand a fee to restore the PC to its former state of operation.
According to research by fraud prevention teams, ransomware is more prevalent across the UK, where scammers test potential viruses before launching them globally. FBI data reveals that rogueware including fake antivirus software and ransom demands are on the increase, netting scammers about $150m annually. The worst aspect of the scam is that, once an affected user has paid to have the software removed, they are handing over all their payment details and account data, ready for unscrupulous thieves to use the data breach to their advantage for further gains.
Holding your technology hostage
When affected by ransomware, it can seem easier to respond to the financial request simply to restore your technology back to working order. However, this is actually the worst possible course of action. It’s important that you take steps to isolate your computer by immediately going offline to prevent any further penetration by scammers.
Once offline, there are a few steps which you may take to remove the problem without falling victim to financial demands. Shut down the computer completely and take it to a reputable technician to have the malicious script removed.
It’s obviously better to avoid infection altogether by practising positive housekeeping on your computer. Install an effective firewall and virus detection, and scan your machine regularly to detect potential threats. Never click on any pop-ups or links in e-mails, if you do not have full confidence about where they originated. Back up all of your data and software regularly to cloud-based storage, to allow you to immediately restore your data should you fall prey to a ransomware attack.
Unlike a real-life hostage scenario, there is no negotiation with ransomware scammers. Through good PC hygiene and strong security, you can avoid your data being compromised, and frustrate potential thieves.